Danish election candidates' passwords, porn habits exposed online days before vote, creating blackmail toolkit
- Ekstra Bladet found candidates' passwords and intimate browsing histories in publicly available data breaches
- Security experts warn foreign intelligence services routinely exploit compromising personal material to pressure politicians
- Denmark votes on March 24, leaving almost no time for candidates to secure their digital footprints
- No public indication that PET, Denmark's security and intelligence service, has warned candidates about the exposure
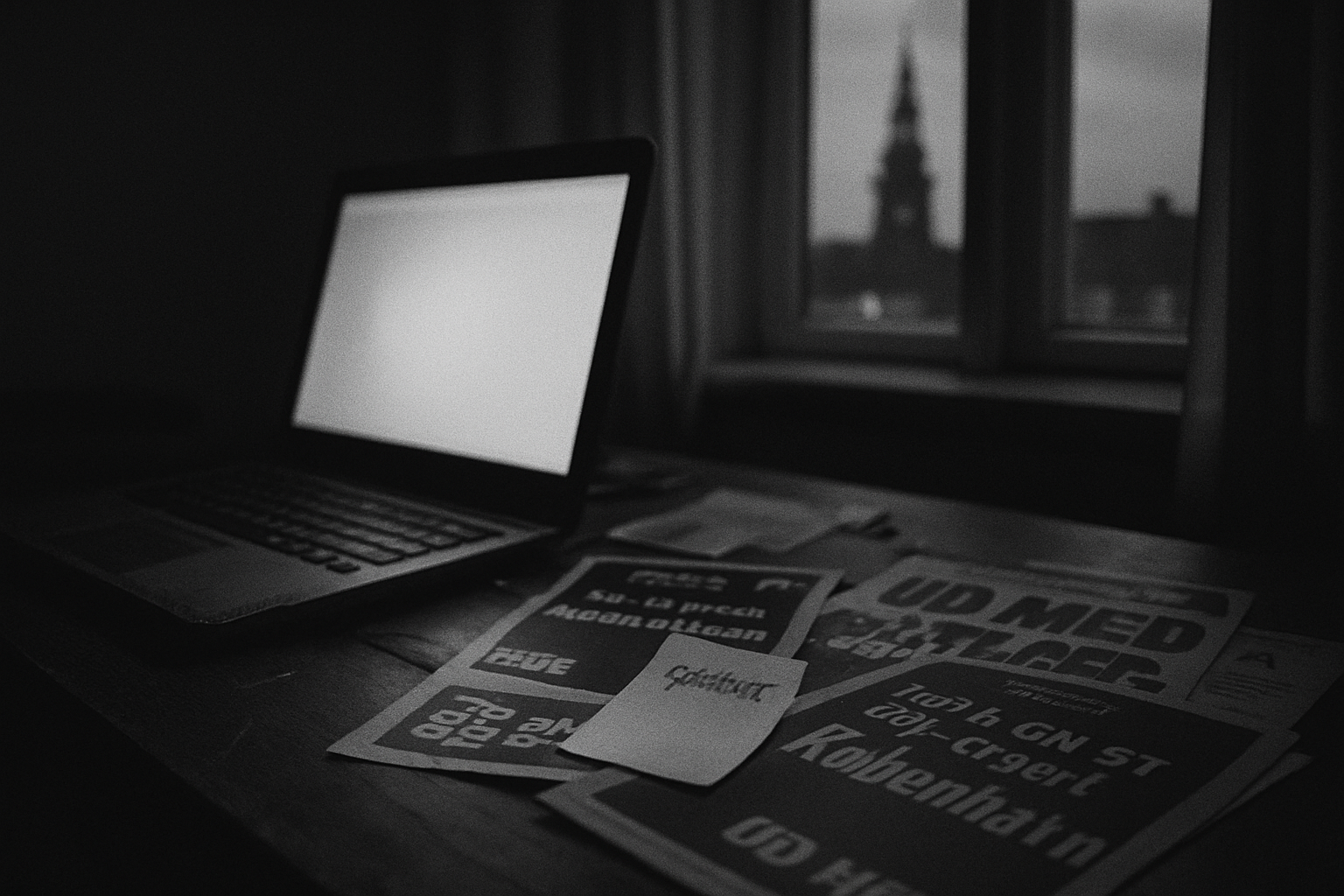
Passwords, login credentials, and pornography consumption habits belonging to candidates in Denmark's upcoming general election are openly accessible online, Ekstra Bladet reports. The data — compiled from publicly available breach databases and online tracking records — amounts to a pre-assembled dossier on people who may hold seats in the Folketing (Danish parliament) within days. Denmark votes on March 24.
The material is not buried on obscure dark-web forums. It sits in databases that anyone with basic technical literacy can query. Ekstra Bladet's investigation found reused passwords, email addresses tied to compromised services, and browsing histories that include visits to pornographic websites — the kind of intimate detail that transforms a minor data leak into a coercion opportunity. Security experts interviewed by the newspaper were blunt: foreign intelligence services routinely harvest exactly this type of material to build pressure files on politicians. A candidate who can be confronted with evidence of embarrassing online activity before they even take office is a candidate who can be steered.
The timing sharpens the problem considerably. With the election days away, candidates have almost no window to audit their digital exposure, change compromised credentials, or prepare responses to potential approaches. The vulnerability is not hypothetical. Nordic security services have repeatedly warned that Russia, China, and other state actors target elected officials and candidates in democratic countries, with Denmark specifically identified as a priority target given its NATO membership, Arctic interests, and hosting of key intelligence infrastructure. PET, Denmark's security and intelligence service (Politiets Efterretningstjeneste), has not publicly stated whether it has briefed candidates on their exposure. Ekstra Bladet's findings suggest that if such briefings occurred, they did not produce visible results.
The broader question is whether this is a uniquely Danish problem or a Nordic-wide one. Sweden, Finland, and Norway all face consequential defence and security votes in the coming period. Candidates and parliamentarians in those countries carry the same digital baggage — reused passwords, old breach data, tracking cookies from sites they would rather not discuss in public. The difference between a politician who votes independently and one who has received a quiet phone call referencing their browsing history is invisible to voters. It is, however, extremely visible to the intelligence service that made the call.
Denmark's candidates are running on platforms covering everything from immigration to defence spending. Their most consequential vulnerability may be one that appears on no ballot: a six-year-old password reused across a dozen services, sitting in a database that any state actor with an internet connection has already downloaded.
Sources: Ekstra Bladet